What Type of Attack Are Stateless Packet Filters Particularly Vulnerable to?
Today we live in the age of impending danger for every device capable of interfacing with the internet. Ingenuitive malware, determined hackers and the e'er-increasing attack surfaces present, not just in computers/phones, merely the innumerable "smart" devices (IOT) has become a modern-day business concern that has to be dealt with by the vast bulk of individuals and industries. One of the most effective ways to deal with unknown cyber security threats is through the apply of dedicated firewalls, designed to protect any & all devices on sensitive internal networks from external attackers or wrongdoers. However, truly effective firewalls need to consistently evolve and confront new threats to businesses, organizations, processes and private individuals.
This is made increasingly difficult by the fact that these targets often possess little time, permit alone the experience/resources necessary to implement & maintain a robust firewall security solution that best suits their requirements. Knowingly or unknowingly, everyone today has a device in their network that serves as a firewall betwixt their devices and the cyberspace, oft provided past their Isp (Internet service provider). However rudimentary the implementation is, these firewalls nevertheless serve as an constructive bulwark to simple and constant attacks perpetrated by bots and motivated hackers. In this commodity nosotros will take a expect at the different implementations of firewalls, their effectiveness and utilize-cases in modern networks.
Stateful Vs Stateless – What'southward the deviation?
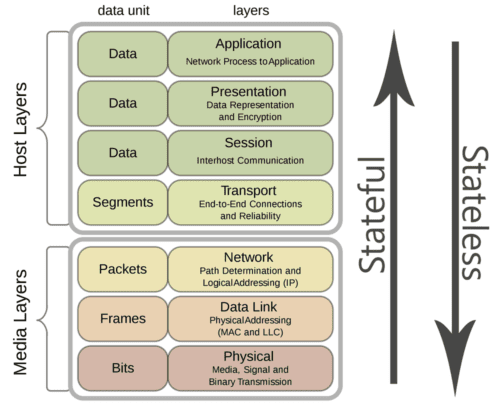
Stateless and stateful firewalls may sound pretty similar with existence denoted with a single distinction, simply they are in fact two very different approaches with diverging functions and capabilities. Parcel filtering potential, is 1 of principle ways in which stateless and stateful firewalls differ from each other. While both firewall implementations perform packet filtering, the differences between them is in the methodology, depth and lengths they become to performing this part.
With these details in mind, well define the principal distinctions between the two every bit this volition help categorize and explicate these implementations and the differences that exist betwixt stateless and stateful firewalls. The main focus volition exist on how they compare to each other in terms of packet filtering performance, levels of security features offered and latent hardware requirements to run these functions. Let's start off by understanding what both stateless and stateful firewalls are, what they are meant to do, and finally how stateless/stateful firewalls implemented every bit a solution compare in the real earth.
Stateless Firewalls
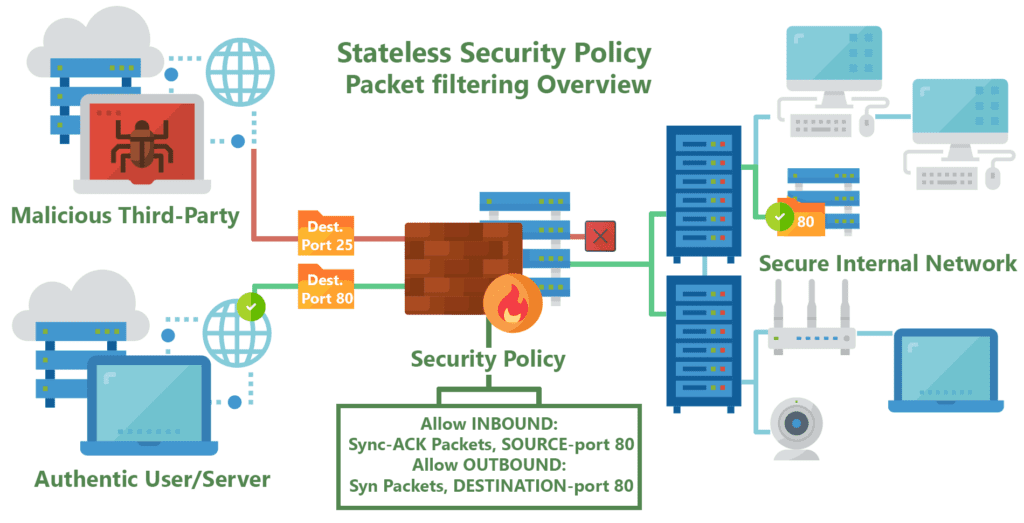
Stateless firewalls are some of the oldest firewalls on the market and have been around for almost equally long as the web itself. The purpose of stateless firewalls is to protect computers and networks — specifically: routing engine processes and resource. They provide this security by filtering the packets of incoming traffic distinguishing between udp/tcp traffic and port numbers. The packets are either immune entry onto the network or denied access based either their source or destination address or some other static information such equally the traffic type (udp/tcp).These days completely stateless firewalls are far and few inbetween.
Today they are virtually commonly seen in the grade of CPE'southward (modems/router combos) given to customers by typical service providers. This equipment, usually given to residential internet consumers, provide simple firewalls using packet filtering and port forwarding functionality congenital on superlative of low-ability CPE's. Providing very basic just powerful security restricting incoming and outgoing traffic useful to protect normally abused ports ofttimes by self-propagating or DDOSing malware, such as ports 443, 53, 80 and 25. This blanket port filtering is mostly implemented using white-lists allowing only a few key ports for application-specific traffic such every bit VoIP, every bit 90% of all internet traffic traverses with the Hyper-Text Transfer Protocol (HTTP) through proxy requests to Domain Name Servers (DNS). In other cases, such as when hosting servers for: multiplayer video games, email/web services, or live-streaming video, users must manually configure these firewalls outside of their default security policy to permit different ports & applications through the filter.
One commonly known pitfall of stateless firewalls is that they are unable to view packets as part of wider traffic and volition inspect them in isolation and are mostly unable to distinguish the myriad of application-level traffic types (such as HTTP, HTTPS, FTP, VoIP, SSH, etc). This can make them susceptible to attacks that are not subconscious inside single packets but spread out across many of them. Stateless firewalls too practice not continue runway of the status of the network as a whole or the connections made to it. However, this does mean that stateless firewalls are much quicker and function more than efficiently due to them only checking the header part of an inspected package.
Stateful Firewalls
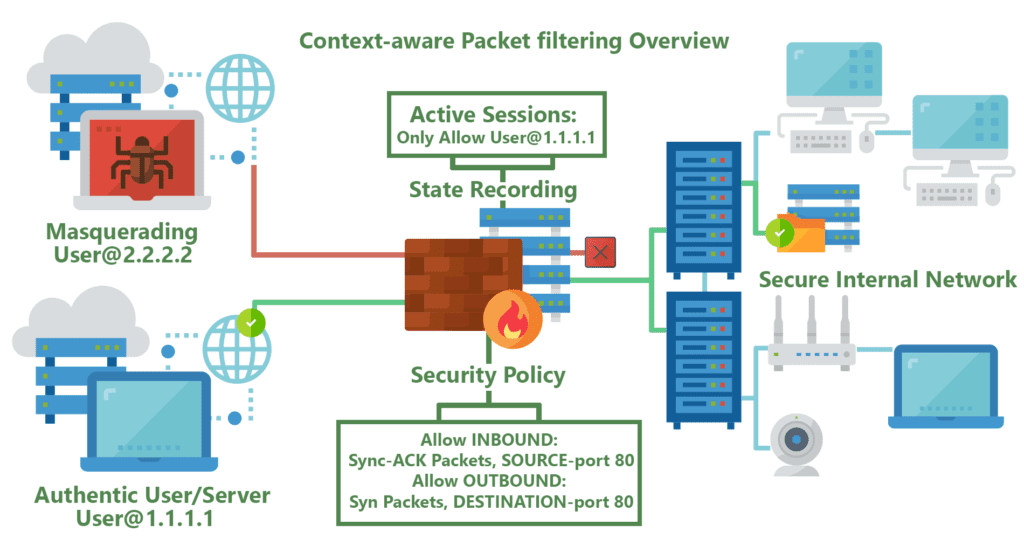
Well-nigh firewalls today offer at least some basic level of stateful monitoring. The master distinction betwixt what can be very rudimentary stateful firewalls, and extremely robust packet-processing solutions , is in the level of protocol support. Greater back up for differentiating between the diverse traffic and protocol types provides firewalls with the efficacy needed to analyze numerous application-level traffic, such as multimedia protocols, datagram protocols, file-transfer protocols, authentication/security protocols so on.
Stateful firewalls are a more avant-garde, modern extension of stateless packet filtering firewalls in that they are continuously able to keep track of the country of the network and the active connections it has such equally TCP streams or user datagram protocol (UDP) advice. The power to acknowledging & utilize the context of incoming traffic and data packets is one of the principle advantages stateful firewalls have over their stateless cousins, allowing them to sympathize how to tell the difference betwixt legitimate and malicious traffic or packets. This ultimately gives stateful firewalls i of the most powerful security tools in modern policies that protect their network connections through the implementation of boosted security procedures for new or ongoing/active connections. In most cases, new connections will demand to introduce themselves to the firewall with what about experts denote as a handshake, earlier being allowed onto the listing of established connections.
Stateful firewalls are not without their vulnerabilities, however. The special handshake involved in establishing new active connections requires a significant increase in software/network connexion complication & the computational power needed to implement them, leaving such firewalls vulnerable to cyber threats such every bit distributed denial of service ( DDoS ) attacks. This threat has been mitigated past many users of stateful firewalls by spreading out a network'south traffic across more firewall appliances , with many using third-party cloud-based service middle-men, in order to reduce the risk and necessary infrastructure.
Which is better?
Every bit is with most things, this varies on a instance-by-case basis, with only the most basic residential users probable served well with their more often than not stateless firewall given past their service providers. When it comes to power-users or business oriented networks, they are all-time served by the powerful stateful firewall implementations provided by dedicated systems running software such as PFSense, Endian or another robust offering. Having said this, while next-gen stateful firewalls offer all of the aforementioned security features nowadays in stateless firewalls, they do not come without the need for price-benefit analysis that should be washed in regards to their feature-prepare and parcel-filtering depth. The as important merchandise-offs and aspects of modernistic firewalls boil down to these requirements:
- Security Level (How secure/sensitive the information & network is)
- Performance Requirements (packets per second, devices on network, application overhead)
- Cost in terms of initial Capital letter Expenditure and ongoing Operating Expenditure for the hardware/software
- Networking & Computing Hardware Requirements along with the underlying infrastructure, space
- Software/Hardware Complexity, in terms of the integrations of upgradability, maintenance & support/EOL

For uncomplicated home use, modern computers have more than than enough power to run robust software-based firewalls on desktop PC'southward for example, but to hands secure the unabridged network using always-on purpose congenital low-power appliances like the NCA-1210 Border Security Appliance is a more cost-constructive solution. Much more stable as a whole, these defended appliances tin can be configured to consistently protect all home & handheld devices like smart thermostats/lights, IP cameras and smart phones from unwanted snooping/tampering by intruders – 24/vii while keeping maintenance, power, infinite and heat footprints to a minimum.
For more advanced usage such as small-scale businesses, power users (online collaborators, home labs, tech enthusiasts, live-streamers) & larger entities, robust stateful firewalls are almost certainly the most viable option to protect sensitive user data, connections and active services. Here the heavier upfront cost of powerful hardware like the FW-8894 NGFW is less meaning compared to the massive issues arising from the amercement of lackluster security. Sub-par security can enable information breaches bringing issues such as: lawsuits, corporate/public epitome taint, service outages and contract/privacy breaches can all easily dwarf whatsoever upfront security investments.
Today businesses looking for the right security solution are best served by experts in the field of network security & hardware/software integration like Lanner. Capable of providing full services similar validation, security module integration & quality balls from the starting time – from the silicon & mill assembly all the way to the business premises .
Source: https://www.lanner-america.com/blog/stateless-vs-stateful-packet-filtering-firewalls-better/
0 Response to "What Type of Attack Are Stateless Packet Filters Particularly Vulnerable to?"
Post a Comment